Fraud Investigations
Overt and Covert Surveillance and Recovery Solutions to Detect, Prevent and Combat Workplace Fraud and Recover Stolen Assets.
There are numerous different types of fraud including asset misappropriation and theft, vendor, accounting and payroll fraud, data theft, staff and client migration, and bribery and corruption. Fraud can be perpetrated either internally by employees, externally by partners or vendors or through a partnership between internal and external sources.
To prevent and combat fraud in your business you need solutions that are either overt and preventative, or covert and designed to catch people in the act or recover assets and funds after the event.
[/fusion_builder_column]
A Recent Increase in Fraud
Fraud is a serious problem in businesses all over the globe. After a few years of decline the issue has started to become more prevalent again in recent years. The American Association of Fraud Examiners (AFCE) estimates that companies lose an average of 5% of annual revenue to fraud. In the UK in 2016 the total cost of fraud exceeded £1,1 billion for the first time since 2011. Due to 7 huge cases of fraud in 2016 the average fraud loss has doubled to £5.2 million. Of course, these are just the cases that are discovered and reported. Some cases are never uncovered and in other instances companies choose not to disclose cases of fraud if it can be legally avoided, as often business owners feel it will cause a scandal and reputational damage to the company.
In addition to the loss in revenue, fraud is a very sensitive area that causes emotions within a company to run high as business owners, management and employees feel betrayed, suspicious and concerned that they may be wrongly implicated in any fraud investigation. Fraud solutions and investigations therefore have to be handled with great diplomacy and tact and of course carried out in accordance with data and privacy laws and without contravening any human rights.
[/fusion_builder_column]
Supply Chain Fraud
Globalisation and multi-party vendor and supplier landscapes have resulted in the Supply Chain industry being particularly susceptible to fraud. Goods are transported over long distances, frequently involving carriage by land, sea and air by multiple third parties in a single journey. The financial transactions are usually high volume, often span several different legal jurisdictions and tend to involve multiple stakeholders. The higher the volume of low to medium cost transactions that are being carried out, the more likelihood there is of a successful fraud being perpetrated, as it is harder to detect when people are making fake transactions. There is opportunity at the warehouse level for misappropriation of physical assets and at senior management level for misappropriation of funds and fraudulent accounting.
Types of Supply Chain Fraud
The main areas of supply chain fraud are:
Product theft and resale or dismantling for parts.
Financial supply chain fraud where internal systems are manipulated and fake transactions are carried out.
Cyber theft and security breaches.
Senior management targeted by bribery and extortion from employees or external third parties.
[/fusion_builder_column]
Collusion & Collaboration
Most commonly supply chain fraud is carried out by collusion between internal members of staff and third-party suppliers. If your business stores and distributes fast moving and highly desirable consumer goods then the most likely fraud will be stock theft at the warehouse level.
Defrauding a company through stock theft requires collaboration between key personnel at various different stages in the supply chain. This could be a supply chain manager who falsifies company records on your internal computer systems, a warehouse or logistics manager who handles the stolen goods and a driver who transports the stolen goods to a destination where a fence can sell them on the black market in their entirety or broken down for parts.
The more organised your supply chain processes are and the more secure you make your technology, the less room there is for people to defraud your business. A powerful, real-time asset tracking, monitoring and recovery system combined with a stringent access control policy and a comprehensive surveillance system is the best fraud deterrent and most effective means of catching the perpetrators.
[/fusion_builder_column]
Asset Misappropriation & Insider Fraud
Asset misappropriation is a blanket term to describe many different types of fraud involving the theft of cash, cheques, expenses, physical assets and services, false procurement and payments, cheque forgery, vehicle misuse, and illness compensation and health insurance fraud by internal employees. that describes a vast number of employee fraud schemes.
It’s essential to have internal checks in place to prevent and detect misappropriation of funds. Although these basic standards may not be an absolute deterrent, the information you collect will assist us in a fraud investigation in the event of an incident.
Vendor Fraud
At the most basic level, it’s imperative to carry out extensive due diligence on your potential vendors. Check to see if they have any relationship to existing employees either familial, from having worked together in the past or through some other connection. It’s important to run checks on vendor documentation and look for red flags such as consecutive invoices, genuine tax and employer ID numbers and mailing and office addresses. Frauds to look out for are over-billing, fixed pricing and bribery.
[/fusion_builder_column]
Accounting & Payroll Fraud
Accounting and payroll fraud are usually perpetrated by more senior employees that work within these departments, where other staff have little or no supervision over their work. The types of frauds you may encounter are funds embezzlement, creation of a fictitious supplier, expenses fraud, lapping and kiting, and account diversion. From a payroll perspective you need to have checks in place to prevent and combat falsified timesheets, theft of one employees paycheck by another or the use of host payroll accounts where an employee leaves the business but his wages are still being paid and diverted to the fraudsters account.
Data Security
Data security breaches make unwelcome headlines and can cause irrevocable reputational damage as people are very concerned about protecting their data privacy. This area is set to become an even bigger priority due to the new General Data Protection Regulation. In addition to copying, masking, encrypting and sub-setting, data protection should be an integral part of your asset, access control and surveillance strategy.
[/fusion_builder_column]
Smarter Technologies Group Fraud Investigations & Solutions
Fraud investigations are delicate operations that need to be tackled with integrity and within the applicable legal parameters. An audit and discreet analysis followed by a covert investigation is often the most effective strategy to uncover fraudulent activity in your business.
When you instruct Smarter Technologies Group to investigate suspected fraudulent activity, you gain the benefit of our teams’ absolute discretion, innovative thinking, state-of-the-art RFID, IoT and GPS surveillance and asset tracking technology that harnesses the power of our Orion Data Network, and 20 years of experience. Our goal is always to bring the situation to a swift conclusion, recover your assets, work with police to secure an arrest and help you protect your brand reputation.
In the UK our staff are trained in P.A.C.E (Police and Criminal Evidence Act). This gives you assurance that, in the event of a prosecution, Smarter Technologies Group understand how to secure and supply official evidence to assist the police in bringing the fraud perpetrators to justice and identify asset ownership for swift recovery.
Our highly trained fraud investigation personnel can seamlessly integrate into your workforce in any environment from office to warehouse to conduct high level, covert surveillance. They are also adept at going undercover and infiltrating the group of fraud conspirators.
[/fusion_builder_column]
[/fusion_builder_column]
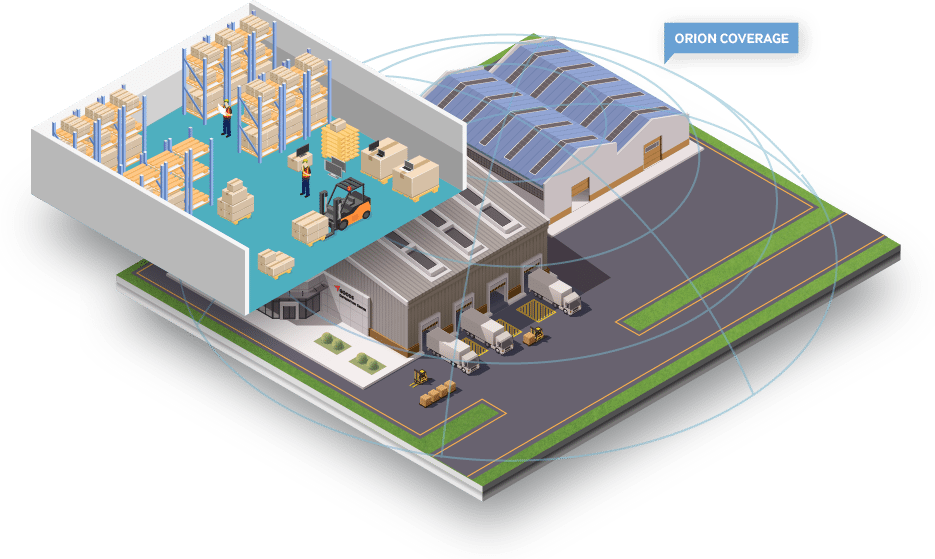
Orion Data Network Asset Monitoring, Tracking & Recovery
Technology and data analysis are key to modern fraud investigations, as big data can show repeated patterns and anomalies that can lead to detection of the fraud and identification of the perpetrator and their illegal systems and processes.
Smarter Technologies Group’s asset tracking, monitoring and recovery solutions are connected to our privately owned and highly secure Orion Data Network, which is a unique combination of Internet of Things enabled sensors, RFID and GPS technology and tags and gateways. It is an excellent tool for covertly or overtly tracking your assets and preventing or identifying warehouse and site theft and fraud.
Pre-defined Data Sets
You can pre-define your required data sets to alert you in real time as to important status information such as your asset location, which member of staff most recently utilised the asset. It can also accumulate and analyse essential business intelligence information from your access control system.
Intelligent Data
It is self -learning technology that can quickly recognise patterns and unusual behaviours to alert you of fraudulent activity and theft and enable fast recovery as well as providing evidence for identification, arrest and conviction. It reports every 15 seconds when your asset is in motion and every 2 minutes when still, to give you total control over your most valuable property and a comprehensive picture of where your key personnel are located and what tasks they are carrying out.
Robust & Long Lasting
Smarter Technologies Group’s Orion asset tracking and security devices come in a wide range of technical and hardware specifications. The devices can be covert or overt and can weigh in as light as 28 grams in applications where a small device is sufficient and depending on device and battery size they can run for up to 5 years on a single battery charge, reporting within a range of up to 10 miles from each Orion Gateway.
[/fusion_builder_column]
Access Control with Orion
Our RFID identification access card solutions allow you to take complete control over which members of staff have access to your site, offices and servers.
[/fusion_builder_column]


[/fusion_builder_column]
Comprehensive Control
Door access control is commonplace in offices all over the world, but our access control solutions provide a much higher level of control and protection for your site, assets, clients and employees. All our solutions are connected to our privately-owned Orion Data Network so you can create data sets and geofenced locations and real-time data feedback on who is accessing different areas of your business throughout the day.
Multi-layered and Easily Integrated
The key is multi-layered security with high levels of integration with other security systems. Our access control solutions allow you to combine identification and access control across your organisation. They enable you to streamline processes such as bringing new employees on board, off-boarding leavers and securely managing visits from external third parties and suppliers. Using one card for multiple applications such as 2 factor device login, canteen payment, printing and building entry, tends to increase its perceived value and mean that personnel are more inclined to look after it properly and not loan it to others.
Secure & Scalable
All Smarter Technologies Group access card solutions and encrypted and encoded and the Orion Data Network cannot be hacked in the way that traditional systems can be so you can rest assured that your card data is secure. The hardware is low cost, robust and reusable and the Orion Data Network facilitates infinite scalability so the system can grow with your business.
All of our solutions are highly customisable and can be designed for use on a mobile device or wearable and can include biometric profiling.
[/fusion_builder_column]
Smarter Technologies Group Fraud Services & Solutions
Fraud prevention
Fraud investigation
Undercover Investigations
Mystery shopper
Asset tracking, monitoring & recovery
Photographic, video, static, mobile, covert and overt surveillance
Site security and access control
IP infringement and fraud
Counter industrial espionage
[/fusion_builder_column]
Benefits
Meet Payment Card Industry Data Security Standards and GDPR requirements
Reduce operating costs by up to 75% more than GSM and CDMA solutions
Real-time reporting every 15 seconds in motion and every 2 minutes when stationary
Ecologically-driven technology for a reduced carbon footprint
Reduced dependency on emergency frequency in times of crisis
Manage, schedule and maintain vehicles and equipment with predictive strategies based on real-time data, to optimise resources and control costs
The Orion signal penetrates walls, metal and underground for application in all areas and environments
Capitalise on Lower Insurance Premiums
Improve Your Customer Experience
Covert and overt tracking, monitoring, recovery and surveillance solutions
Prevent and detect fraudulent activity
Manage Your Corporate Reputation
GPS and non-GPS tags for near real time tracking of vehicles and people
Unique analogue beacon mode for asset recovery with hand-held equipment
Long range site monitoring from 500 meters to 10km+ radius of each Gateway
Intelligent Data with a sophisticated suite of API’s
[/fusion_builder_column]
Start tracking your assets
[/fusion_builder_column]

LET’S TALK
Our experts are waiting to answer your enquiries and help design a solution for you.
Call on 0330 223 5000

VISIT US
Smarter Technologies Group 1 Austin Park, Yeoman Road, Ringwood, BH24 3FG, United Kingdom
Fraud Investigations enquiries
Fill out the contact form and let us know how we can help you. Our experts are waiting for you.
Our experts are waiting to answer your enquiries. Smarter Technologies will never use any of the details you supply us for any other purpose.
